You Know About Phishing. So Why Does It Still Work?
Most people can spot a bad phishing email in seconds.
Misspelled words.
Weird senders.
Obvious links.
And yet, phishing remains one of the most successful cyberattack methods in the world.
Not because people are ignorant.
Not because warnings don’t exist.
But because phishing no longer relies on ignorance.
It relies on human behavior under normal conditions.
Phishing works not when you’re careless—but when you’re busy, tired, trusting, or emotionally engaged.
That’s why awareness alone hasn’t killed it.
Phishing Didn’t Disappear — It Evolved
Early phishing emails were crude.
Today’s phishing is refined, contextual, and deeply human.
Attackers study:
- Daily routines
- Workplace workflows
- Emotional triggers
- Brand trust
They don’t guess anymore.
They blend in.
Many phishing emails now look identical to legitimate messages from platforms like Microsoft, Google, or Amazon.
The goal isn’t to trick everyone.
It’s to succeed once.
The Core Truth: Phishing Targets the Brain, Not the Inbox
Phishing is a form of social engineering, not a technical hack.
It works because it exploits:
- Trust
- Urgency
- Authority
- Familiarity
When a message triggers emotion, logic temporarily steps aside.
And attackers know exactly which emotional buttons to press.
The Emotional Hooks That Still Catch People
Modern phishing emails are engineered around predictable emotional states.
Common triggers include:
- Urgency: “Action required within 24 hours”
- Fear: “Unusual activity detected”
- Relief: “Issue resolved — confirm here”
- Curiosity: “You were mentioned in a document”
- Authority: “Compliance team request”
These emotions reduce critical thinking—even in smart, cautious people.
Why “Smart People” Fall for Phishing Too
Phishing success isn’t about intelligence.
It’s about context.
Smart people:
- Move quickly
- Handle high volumes of messages
- Trust familiar systems
- Rely on pattern recognition
Attackers design phishing emails to fit seamlessly into expected workflows.
When something looks routine, the brain switches to autopilot.
That’s when mistakes happen.
The Familiarity Trap: When Normal Looks Safe
Phishing works best when it feels boring.
A fake invoice.
A calendar invite.
A password reset you weren’t expecting—but could plausibly receive.
Attackers mimic:
- Email signatures
- Language tone
- Formatting styles
- Timing patterns
When an email matches what you expect, scrutiny drops dramatically.
Real-Life Phishing Examples That Still Succeed
The Fake Shared Document
Emails claiming a document was shared via Dropbox or Google Drive are among the most effective phishing formats.
Why?
Because people share documents every day.
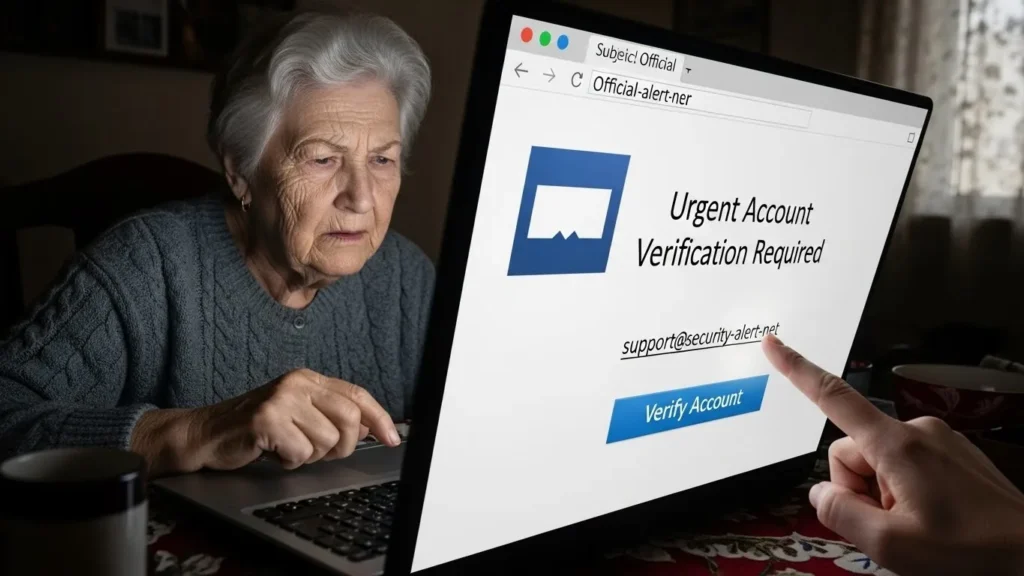
The “Security Alert” Email
Messages claiming account issues prompt immediate action—especially when they appear to come from trusted services.
The Internal Work Email
Business email compromise attacks impersonate colleagues or executives, relying on hierarchy and urgency.
These emails don’t look suspicious.
They look like work.
Why Training Alone Hasn’t Solved Phishing
Many organizations train employees to spot phishing.
And yet, phishing persists.
Why?
Because training focuses on what phishing looks like, not how people behave under pressure.
Most successful phishing attacks occur when:
- Someone is multitasking
- Someone is tired
- Someone is emotionally triggered
- Someone feels rushed
No training slide overrides human instinct in those moments.
Old Phishing vs Modern Phishing
| Feature | Traditional Phishing | Modern Phishing |
|---|---|---|
| Language | Poor grammar | Polished, natural |
| Design | Obvious scams | Brand-accurate |
| Targeting | Mass emails | Context-aware |
| Timing | Random | Perfectly timed |
| Detection | Easier | Subtle |
Phishing didn’t become smarter.
It became more human.
Why This Still Matters (And Always Will)
Email remains the backbone of:
- Work
- Finance
- Identity recovery
- Communication
As long as email exists, phishing will exist.
Because phishing doesn’t exploit software.
It exploits trust systems.
And trust is necessary for digital life to function.
Common Mistakes That Keep Phishing Effective
Even cautious users make these errors:
- Clicking links instead of navigating manually
- Trusting sender names instead of email addresses
- Acting quickly to “fix” issues
- Reusing passwords after alerts
- Assuming filters catch everything
Phishing thrives in assumptions, not ignorance.
Simple Habits That Dramatically Reduce Risk
You don’t need paranoia.
You need consistency.
Actionable habits:
- Pause when urgency appears
- Check sender domains carefully
- Hover over links before clicking
- Log in directly instead of using email links
- Treat unexpected requests as suspicious—even if familiar
Most phishing fails when users slow down for 10 seconds.
The One Question That Stops Most Phishing Attacks
Before acting, ask:
“Was I expecting this?”
That single question disrupts the emotional momentum phishing relies on.
If the answer is no—pause.
Why Phishing Success Rates Won’t Drop to Zero
Even with perfect awareness:
- Humans get tired
- Context changes
- Emotions fluctuate
Phishing works because it aligns with how humans naturally operate, not because people are careless.
The goal isn’t perfection.
It’s reducing exposure enough that attacks fail more often than they succeed.
Key Takeaways
- Phishing succeeds by exploiting human behavior, not ignorance
- Familiarity and urgency are its strongest weapons
- Awareness helps—but habits matter more
- Smart people fall for phishing in normal moments
- Small pauses and verification break most attacks
Frequently Asked Questions
1. Why do phishing emails still work if everyone knows about them?
Because phishing targets emotion and routine, not knowledge. Awareness doesn’t override instinct under pressure.
2. Are phishing emails becoming more sophisticated?
Yes. They’re more polished, contextual, and timed to feel routine rather than alarming.
3. Is spam filtering enough protection?
No. Filters help, but attackers design emails to bypass them. Human judgment remains critical.
4. What’s the biggest red flag in phishing emails?
Unexpected urgency—especially when it pushes you to act immediately.
5. Can phishing ever be completely eliminated?
Unlikely. As long as trust-based communication exists, phishing will adapt.
Conclusion: Phishing Works Because It Feels Human
Phishing emails don’t succeed by being obvious.
They succeed by feeling normal.
They arrive when you’re busy.
They sound like people you trust.
They ask for things you regularly do.
Understanding this isn’t about fear—it’s about clarity.
Once you see phishing as a psychological play instead of a technical trick, it becomes much easier to spot—and much harder to fall for.
Disclaimer: This article is for general informational purposes only and does not replace professional cybersecurity guidance for specific situations.

Natalia Lewandowska is a cybersecurity specialist who analyzes real-world cyber attacks, data breaches, and digital security failures. She explains complex threats in clear, practical language so everyday users can understand what really happened—and why it matters.
Pingback: What Happens Inside a System During a Cyber Attack — The Silent Sequence You Never See
Pingback: How Ransomware Attacks Spread So Quickly — The Chain Reaction Most People Never See
Pingback: Antivirus Alone Won’t Protect You Anymore — Here’s What You Actually Need